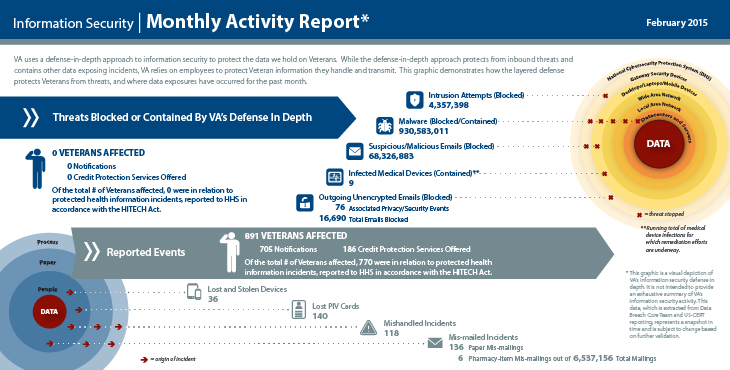
VA serves Veterans and their families by maintaining robust information security controls, utilizing a multi-layered, “defense in depth,” approach to securing Veteran data. However, no organization, no matter how advanced its safeguards, is immune to risks associated with simple human error. When an incident that violates a VA security or privacy policy occurs and VA safeguards fall short, VA has a comprehensive incident response plan to proactively address the situation and limit risk and recovery time.
What is an Incident?
As a Veteran service provider of both health care and benefits services, VA retains personal information on millions of Veterans and their family members. When that information is exposed to potential unauthorized access, VA considers it an information security or privacy incident. Examples of these incidents include:
- The disclosure of sensitive information to unauthorized persons
- An attempt to gain unauthorized access to a VA system or data
- Documents containing sensitive information left unattended in an unsecured location
- The improper disposal of VA documents or data
The Incident Response Process
VA protocol requires VA employees to immediately report any suspected incident to local information security personnel. Incidents are then forwarded to VA’s Incident Resolution Team. This team coordinates with local personnel and other VA employees to determine the potential impact of the incident. If necessary, incidents are then escalated to VA’s Data Breach Core Team. Incidents are entered into the national incident tracking database, and major incidents are reported to the Secretary in a daily incident report and to Congress once a month. Over the last 12 months, VA has refined and improved the efficiency of this process, significantly decreasing the average incident response time.
What This Means for Veterans
When it comes to information security, VA takes the security of Veteran data seriously – the protocols and safeguards put in place allow VA to uphold its mission of protecting and serving those who have so bravely served this country. Its layered cyber defenses protect information from evolving cyber threats, but VA also understands the importance of having rapid, organized reactions when information is put at risk. VA’s response to an incident begins immediately after detection or reporting, and follows through with detailed reporting to Veterans and Congress. If VA’s defense in depth strategy should fall short, it works to quickly notify affected Veterans and offer credit monitoring support to further ensure the security of personal information.
VA’s proactive approach to information security and incident response has led to a safer network for Veterans and their families. With the addition of mobile apps and telehealth procedures, VA has continued to upgrade and expand its security procedures with the health and safety of Veterans in mind.

Topics in this story
More Stories
The VA Health and Benefits mobile app is modernizing how Veterans access and manage their health care and benefits information.
Learn how you can guard your VA online health information against scammers and online threats when using My HealtheVet or VA apps.
VA has added a seamless online ordering system for CPAP supplies in addition to hearing aids, enhancing how Veterans access and manage crucial supplies, making the process more accessible and efficient.